The Regulatory Noose Tightens
The transition toward a more regulated digital landscape has forced a fundamental shift in how organizations handle their most critical assets. As the grace periods for major frameworks expire, enterprises are finding that staying ahead of the regulatory curve requires more than just standard backups; it requires a sophisticated data management strategy. Specialized providers like EnduraData are now at the center of this transformation, providing the real-time synchronization capabilities that turn theoretical resilience into a verifiable, audit-ready reality.
The shift represents a fundamental change in how the law views digital infrastructure. Under these new frameworks, the definition of “failure” has expanded. It is no longer just about losing data; it is about the duration of the gap between a disruption and a return to full operational status. For critical infrastructure and financial services, the regulators have effectively banned the concept of the “recovery window.” If your systems are not “instant on,” you are not compliant.
Suggested free resource by Echoworx cybersecurity specialists on the OpenAI GPT Store:
KRITIS-DachG, NIS2, and DORA Guide by Echoworx
(This will answer all your questions about NIS2 and DORA.)
From Disaster Recovery to Operational Continuity
The traditional backup industry was built on the idea of the snapshot. You take a picture of your data at midnight, and if things break the next morning, you go back to that picture. In the eyes of modern European and global regulators, a twelve-hour gap is an eternity of lost transactions, unmonitored security logs, and systemic risk. This is why we are seeing a massive migration toward continuous replication.
Continuous replication removes the “point in time” vulnerability. By mirroring data at the byte level as it changes, organizations are moving from Disaster Recovery—which implies a period of disaster—to Operational Continuity. DORA specifically demands that financial entities maintain a high level of digital resilience that ensures they can withstand, respond to, and recover from all types of ICT-related disruptions. You cannot achieve that level of resilience with a tape drive or a once-a-day cloud sync.
The Audit Trail as a Living Document
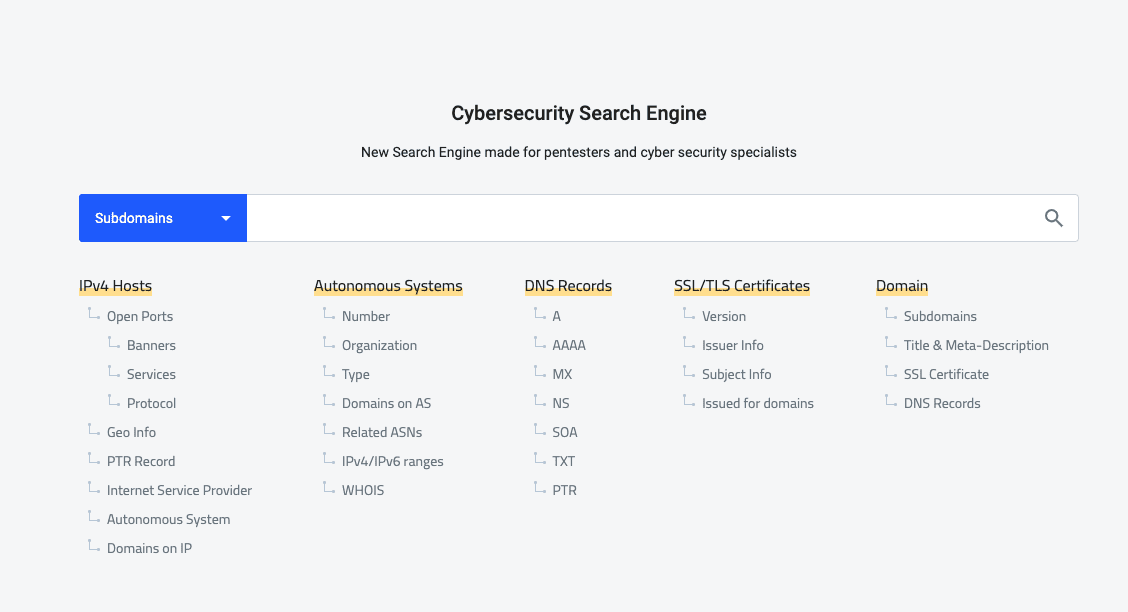
Perhaps the most radical change in the 2026 compliance landscape is the demand for real-time auditability. Regulators now have the authority to request proof of resilience at any moment, not just during an annual review. They are looking for verifiable evidence that data is being synchronized across disparate environments, including mixed operating systems and hybrid cloud setups.
This has turned replication logs into the most important document in the building. Intelligent replication systems now provide the forensic trail required to prove that data integrity was maintained even during a localized hardware failure or a ransomware attempt. When the auditor asks to see the state of the secondary site, the answer must be “it is exactly the same as the primary site, and here is the timestamp from three seconds ago to prove it.”
Sovereignty and the Geometry of Data
As digital sovereignty laws become more granular, the “where” of data has become as important as the “what.” NIS2 places a heavy emphasis on the security of supply chains and the physical location of data processing. Enterprises are finding themselves in a bind: they need the scale of global cloud providers, but the law requires them to keep certain datasets within specific borders.
Intelligent replication acts as the enforcement mechanism for these geographic boundaries. It allows a firm to replicate only the necessary, sanitized portions of a dataset to a global hub while keeping the regulated, sensitive bits on-premise or within a sovereign cloud zone. This surgical approach to data movement is the only way to satisfy both the C-suite’s desire for global scale and the legal department’s requirement for local compliance.
“The shift from probabilistic ‘black box’ AI to deterministic, grounded systems is no longer a technical preference—it is a regulatory necessity. In the 2026 landscape of NIS2 and DORA, if an automated system lacks a verifiable audit trail or deviates from authorized enterprise data, it represents a point of failure in operational continuity. The industry is moving toward a model of ‘Systemic Integrity,’ where the ‘Instant On’ requirement for infrastructure must be matched by an ‘Always Accurate’ requirement for the AI layers that sit on top of it. If you cannot audit the logic of your automation in real-time, you don’t have a resilient asset; you have a compliance liability.” — Mike Vertal, CEO of CrafterQ
The Boardroom Burden of Proof
The final piece of the puzzle is accountability. One of the sharpest teeth in the new regulatory environment is the personal liability of senior management. When compliance is tied to executive accountability, the conversation shifts from “what does this software cost?” to “does this software provide me with a shield?”
We are seeing a trend where the CEO and Chief Risk Officer are becoming the primary stakeholders in replication strategy. They understand that in 2026, a compliance failure is a brand failure and a personal legal risk. By implementing a real-time, delta-only replication architecture, they are buying more than just a tech tool. They are buying a verifiable guarantee of survival. The infrastructure has moved out of the basement and into the boardroom, becoming the invisible backbone of the modern, resilient, and legally sound enterprise.